
How to spot a data breach
The words Incident and Breach can be quite worrying, the connotation behind them being especially…

The words Incident and Breach can be quite worrying, the connotation behind them being especially…
From 14 February we’re sharing the love by introducing Microsoft Sway. This is an application…

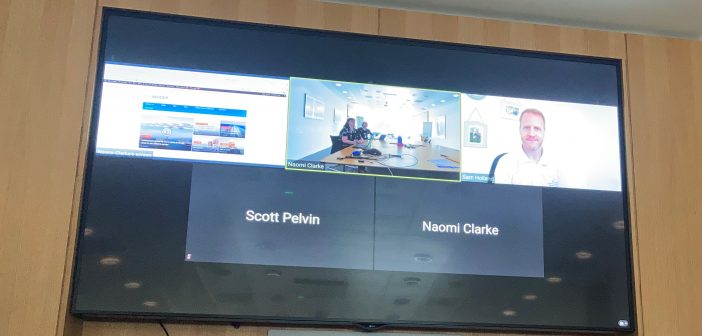
Today Technology is offering demonstrations on how to use Neat bars and frames, which are…

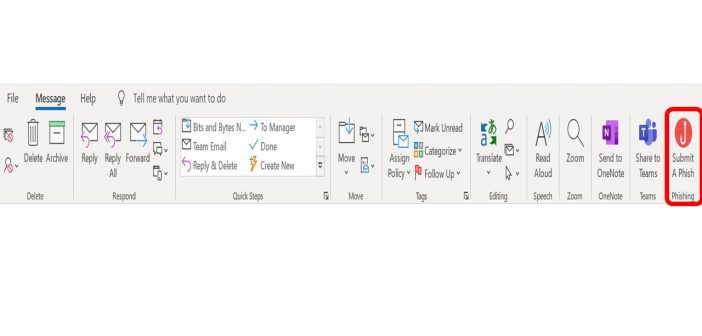
Resolve to report phishing with the “Submit a Phish” button Did you know milestones like…
How Scammers Use Psychology to Trick Victims into Disclosing Sensitive Data According to the FBI,…
Using MFA on your Mobile device We’re always looking to improve the security of the…

How to Protect yourself from the Latest Holiday Cyber-scams While cinnamon, spice and everything nice…
How you access Condeco and M365 on mobile is changing…. In the Technology team we’re…
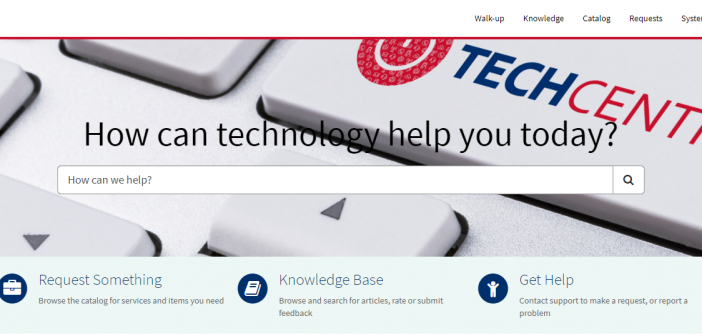
Our new online, IT service portal, The TechCentre, is now live! The TechCentre is an online…

Come and join* us on Wednesday 9 November when Josh Weinstein will be launching our…

On Tuesday 8 November, our new IT Request system – The TechCentre goes live! Make…
On 26 October we’re hosting the Cyber Security Event at Carnival House, in the Atrium…
On 26 October we’re hosting the Cyber Security Event at Carnival House, in the Atrium…

We’ve been working on something exciting in Technology. It’s called the TechCentre. What’s that you…

Does your systems access matter to you? It does to us. We’re the Identity and…

Hackers have limitless opportunities when using social media, learn how to stay safe online! It…

Social media hacks are on the rise, meaning the risk to your private information is…

Though threats to cyber-security may regularly make the news, we as a company know how…

How scammers are using QR codes to steal personal information With contactless interactions becoming the…

How scammers are using QR codes to steal personal information With contactless interactions becoming the…

Are Robots Trying to Steal Your Data? A new fake chatbot phishing trend is emerging, learn…

The words Incident and Breach can be quite worrying, the connotation behind them being especially…

Did you know about 30,000 spoofing attacks happen per day? The term “spoof” might not…

Did you know even one cyber-security lapse within our global supply chain can put us…
Messaging platforms like WhatsApp are a hotbed for conniving crooks trying to steal your personal…

If you receive a text from your boss, it’s most likely important but instead of…

The ‘Submit a Phish’ button joined us last November, with many of you using the tool…
Great news for collaborative working – it’s now even easier to connect with colleagues who…

We would like to invite you to check that your contact details are showing correctly…

It is a very bad, no good, week for hackers. That’s because this fun and…
Fishing is a pastime enjoyed all over the world and is also a global industry. …

What would a celebration for International Data Protection Day be, without a degree of temptation,…
Data, Risk and Privacy are all subjects that some people feel can be quite dry.…

A big thank you for all your questions from all of us here…

Today’s International Data Protection Day, when companies carry out activities globally to raise awareness about…
It’s that time of the year when we are setting goals and looking at what…
Have you just read the latest Bits & Bytes and find yourself inspired to share…

Last year we rolled out Teams , a collaboration app that helps you stay organised…

Ship to shore – always secure is an ongoing priority. To help us protect our Guests,…

Teams is now live! From today all shoreside colleagues, our Onboard SMT and some select…

This time of year is filled with holidays, celebrations, time spent with loved ones and…
How to Encrypt Emails and Stay Cybersecure Email is one of the most common ways…
Keeping you up to date with where we are at so far in the Microsoft…
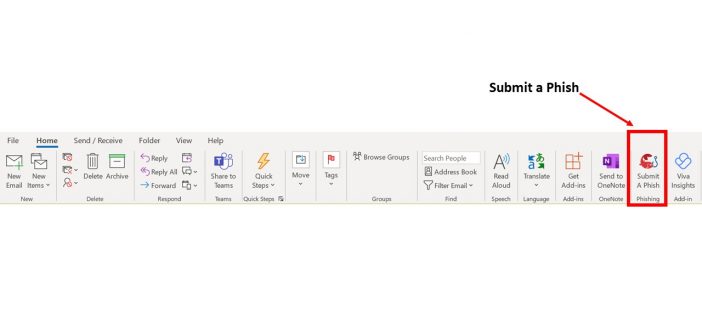
A Phish is a suspicious looking email that could be asking you to click on…

What Hackers Don’t Want You to Know Now it is more important than ever to stay…

What Hackers Don’t Want You to Know Now it is more important than ever to stay…
Keeping you up to date with where we are at so far in the Microsoft…
Keeping you up to date with where we are at so far in the Microsoft…

It’s easier for cybercriminals to hack a human than to hack a company network. That…

When asking ourselves, ‘What sparks joy?’” The last thing that comes to mind is document…

How many hours have you spent sifting through old files, only to find yourself wondering…

Keeping you up to date with where we are at so far in the Microsoft…

From 17 September the majority of shoreside colleagues (excluding Mumbai, QM2 Refit Team, Cognos Users,…

Keeping you up to date with where we are at so far in the Microsoft…

You may be wondering what’s happening with our journey to bring you Microsoft Office 365…

There’s a reason phishing is one of the most common cybercrimes – it works. Phishing…

We’re delighted to introduce our new Tech Bar to support all of your technology needs. If…

We’ve started our Microsoft 365 implementation. Given the shift to remote working, Microsoft 365 will form the…

As we look to return to service we need to be mindful of data usage…
If we think back to before Covid-19, when we worked at Carnival House, the way…

Everyone needs a reminder on how to stay secure – it’s easy to feel safe…

Our story starts on 22 May 1978 when Mike Blackwell started working at Cunard Line.…

This month we’re sharing wellbeing stories from people across the business to help inspire you…

The first line of defence to any company is its people. Scammers know this -…
Ship to shore – always secure is an ongoing priority. To help us protect our Guests,…

Our industry has seen a huge rise in cyber attacks looking to exploit COVID-19 through…

A big congratulations to Cristina Munoz who was a shortlisted finalist for the ‘Above and…

What were my words last week? We never think it’s going to happen to us…

Remote working is becoming more and more common in the workplace. It’s great to have…

Well hello there – I’m your friendly neighbourhood hacker! I can introduce myself to your…

Good news! We’re going to be making a significant cost saving by moving our phone…

Did you know that the most popular form of cyber attack is through phishing emails? …

This isn’t a sad story. (I can say that now.) A few years ago I…
Storing Emails As part of the suite of changes due to the General Data Protection…
As part of the suite of changes due to the General Data Protection Regulation (GDPR)…
As part of the suite of changes due to the General Data Protection Regulation (GDPR)…
During 2018 a project team was established to upgrade our CORe application to the latest…
Looking after our information became a hot topic last week in Carnival House. Many of…
Information security is about to become the hottest topic in Carnival House! Join Josh at…
The star-spotters among you might have noticed camera crews in Carnival House or on board…
We’ve identified six key information security topics. These are the risk areas most likely to…
Not sure how you can keep our information secure? Over the next three months, we’ll…
It’s the second ‘S’ in HESS, but what exactly is Security? There are four key…